The End of Oil Wars: How Renewable Energy + Causal AI Can De-Risk Nations
Energy policy is no longer just about electricity. It is about security, economic stability, public health, and technological sovereignty.
This article introduces a new framework — The Renewable Security Model — and explains how causal AI can help policymakers understand the chain of impacts from renewable investment to peace and prosperity.
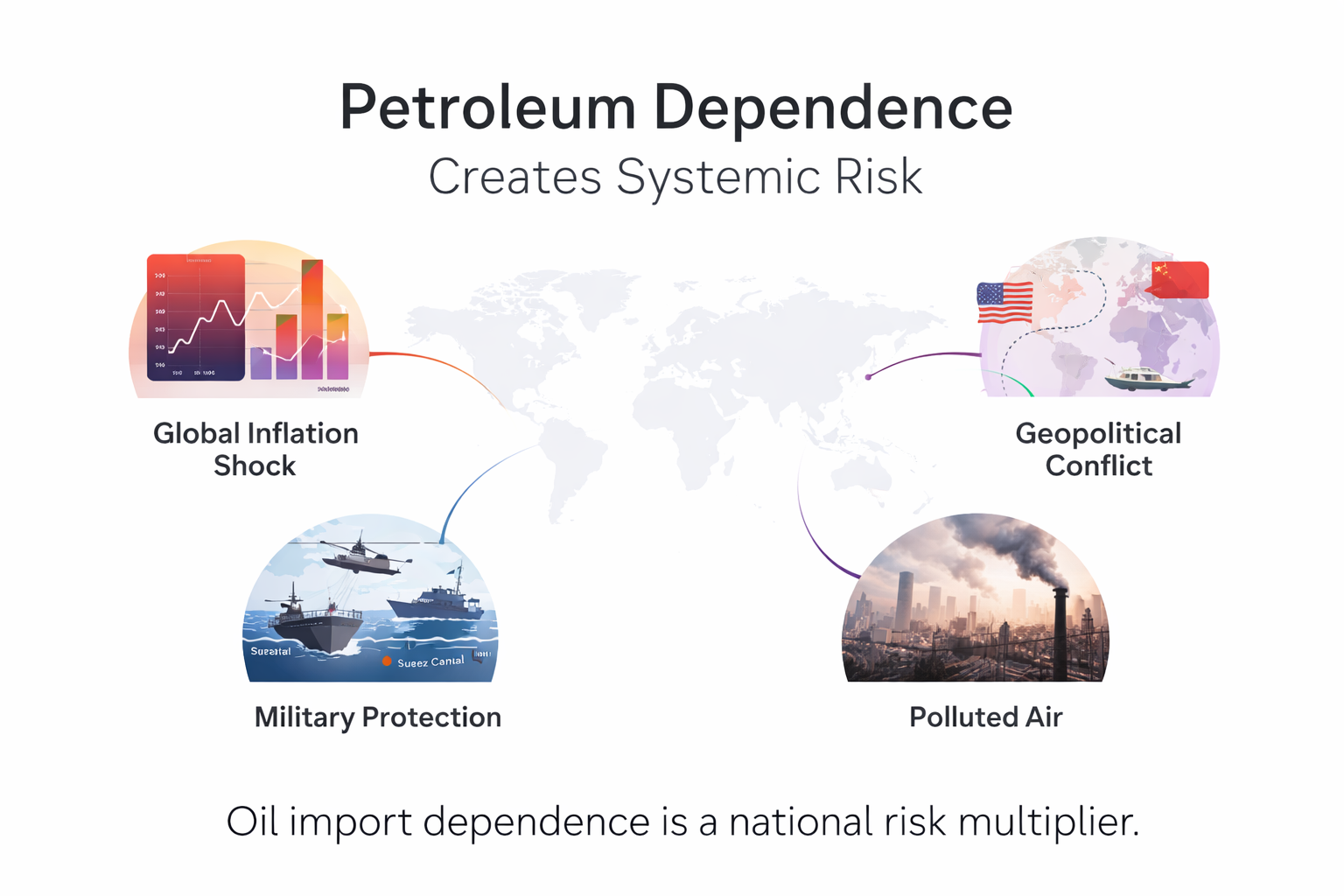
Stage 1 — The Problem: Petroleum Dependence Creates Systemic Risk
Countries heavily dependent on oil imports face multiple overlapping risks:
Exposure to geopolitical conflict
Inflation shocks from fuel prices
Trade deficits and currency instability
Pollution and public health burdens
Defence spending tied to energy insecurity
These risks are often treated separately. In reality, they are causally linked.
Key insight: Oil dependence is not just an energy issue — it is a national risk multiplier.
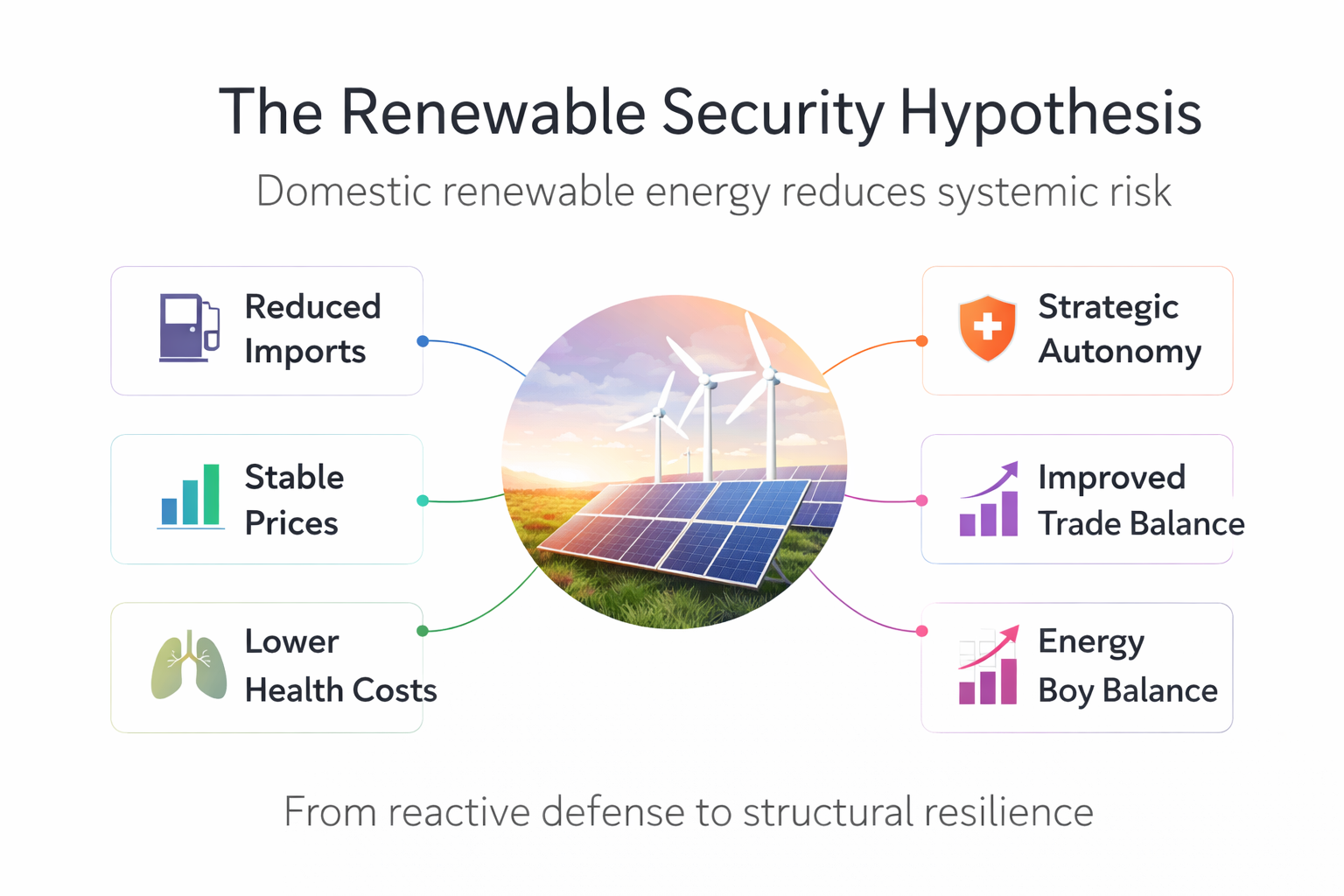
Stage 2 — The Renewable Security Hypothesis
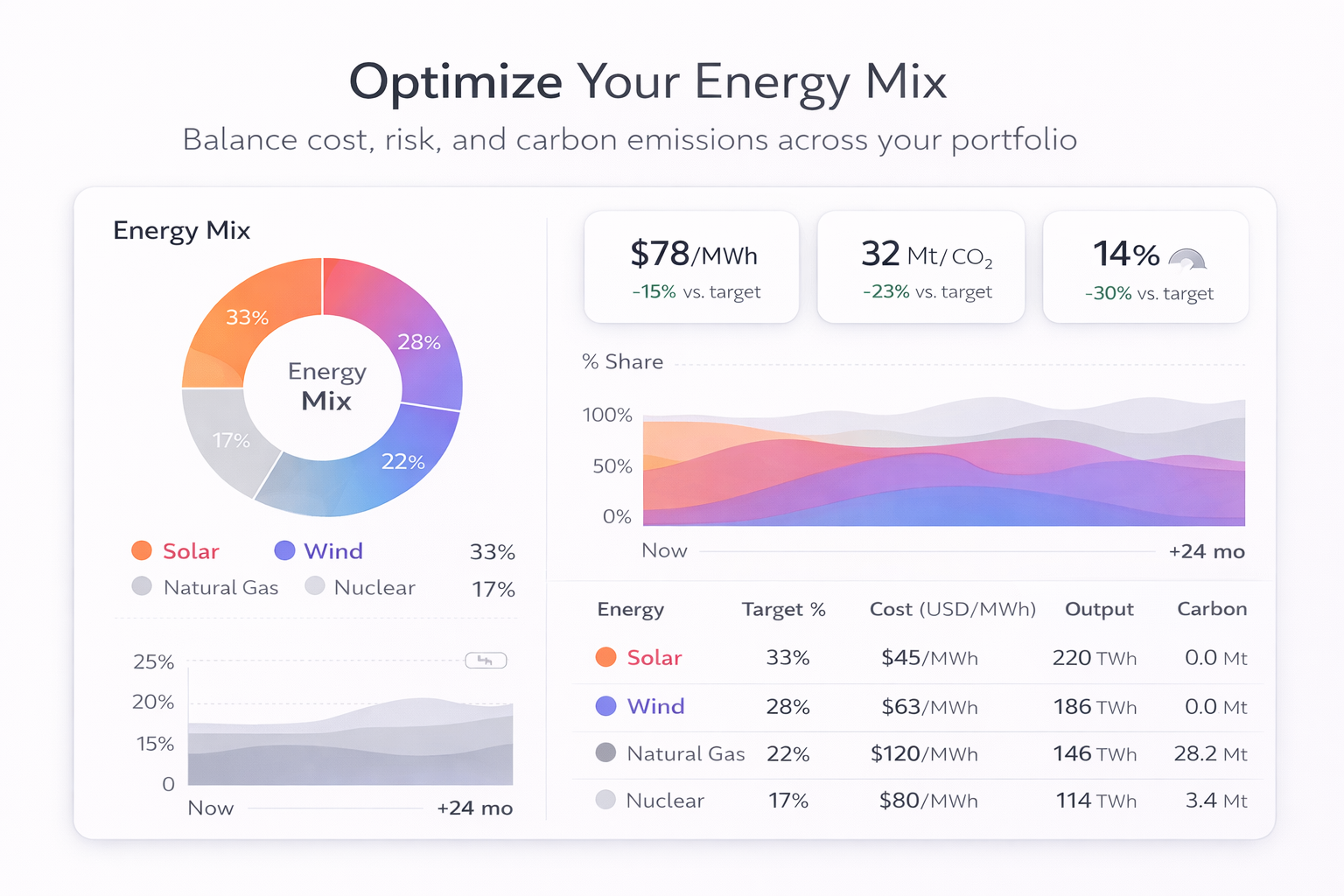
The Renewable Security Model proposes that domestic renewable energy reduces systemic risk by:
Lowering fuel import dependence
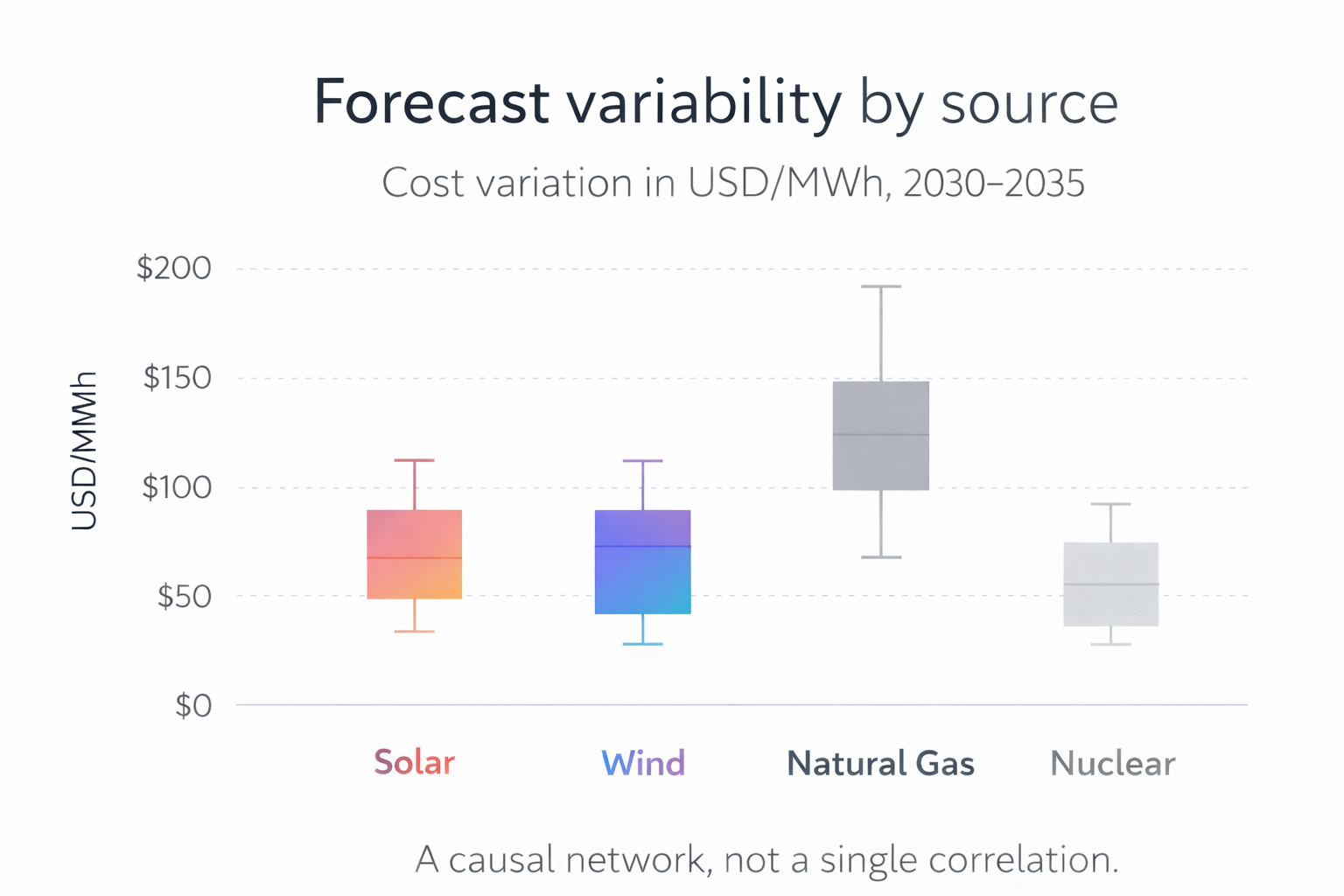
Stabilizing energy prices
Reducing pollution-related health costs
Improving trade balance
Increasing strategic autonomy
This shifts the concept of security from reactive defence to structural resilience.
Structural security = domestic energy + stable costs + resilient infrastructure.
Stage 3 — Introducing Causal AI
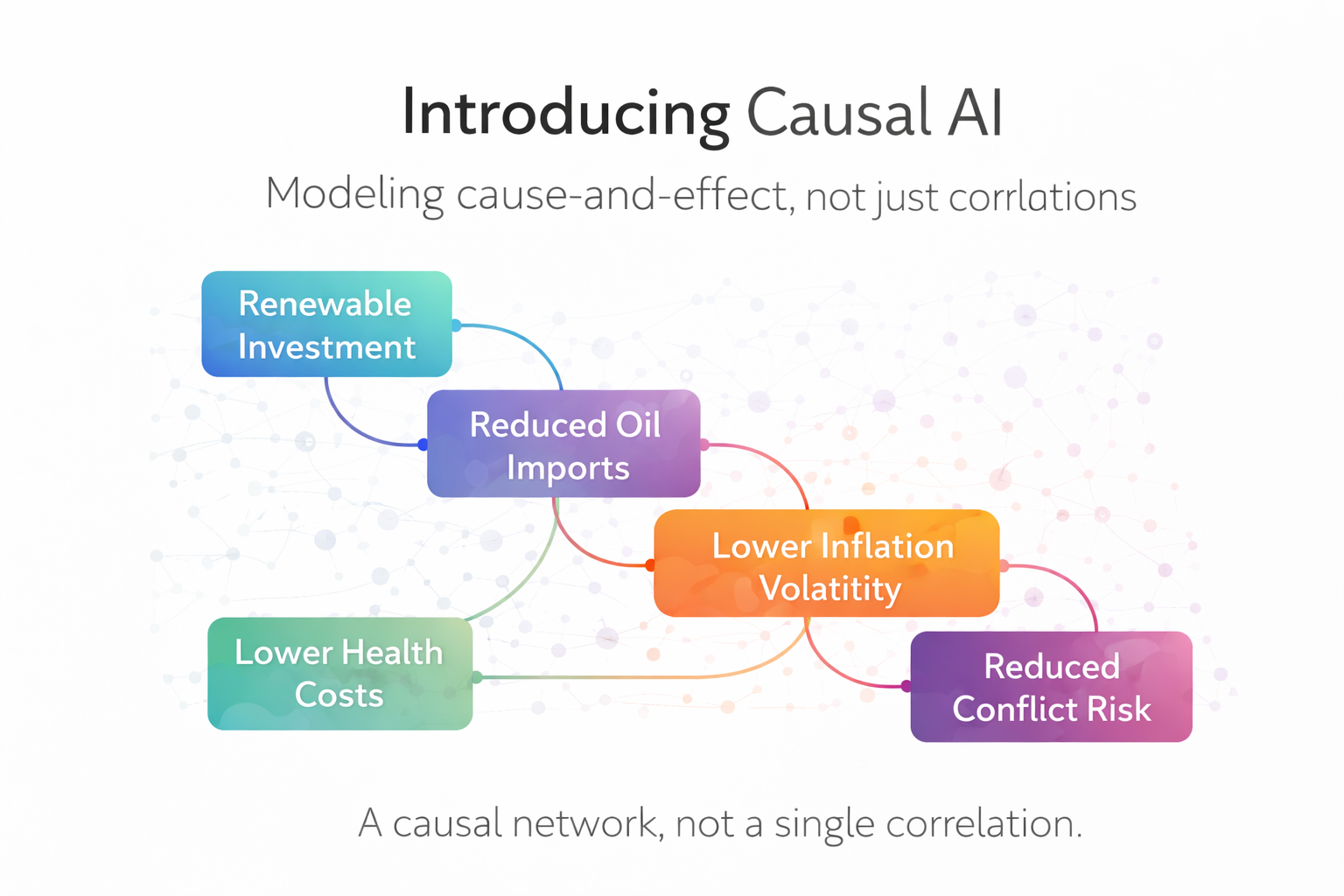
Traditional models rely on correlations. Causal AI instead models cause-and-effect relationships.
Example causal chain:
Renewable investment → reduced oil imports → lower inflation volatility → improved economic stability → reduced conflict risk
This is not a single relationship. It is a causal network.
Causal AI allows us to test counterfactuals: What happens if a country doubles renewable investment? What happens if defence spending increases instead?
Stage 4 — The Defence Opportunity Cost
Many countries spend heavily on defence partly because of energy insecurity:
Protecting supply routes
Managing geopolitical risk
Stabilizing fuel shocks
The Renewable Security Model asks:
What if renewable investment reduces the need for some of these costs?
This becomes a “Guns vs Grids” comparison:
Spending to manage vulnerability vs
Spending to remove vulnerability
Stage 5 — The Renewable Dividend
As countries invest in renewables, they generate a Renewable Security Dividend:
Avoided oil imports
Lower health costs
Reduced price shock losses
Improved productivity
Export opportunities
These savings can be reinvested strategically.
This is where the model evolves from risk reduction to growth acceleration.
Stage 6 — Reinvesting in AI Infrastructure
The next step in the model is reinvesting renewable dividends into:
AI infrastructure
digital grid optimization
industrial automation
logistics optimization
smart governance systems
AI increases productivity across the economy.
Cheap clean energy + AI = competitive advantage.
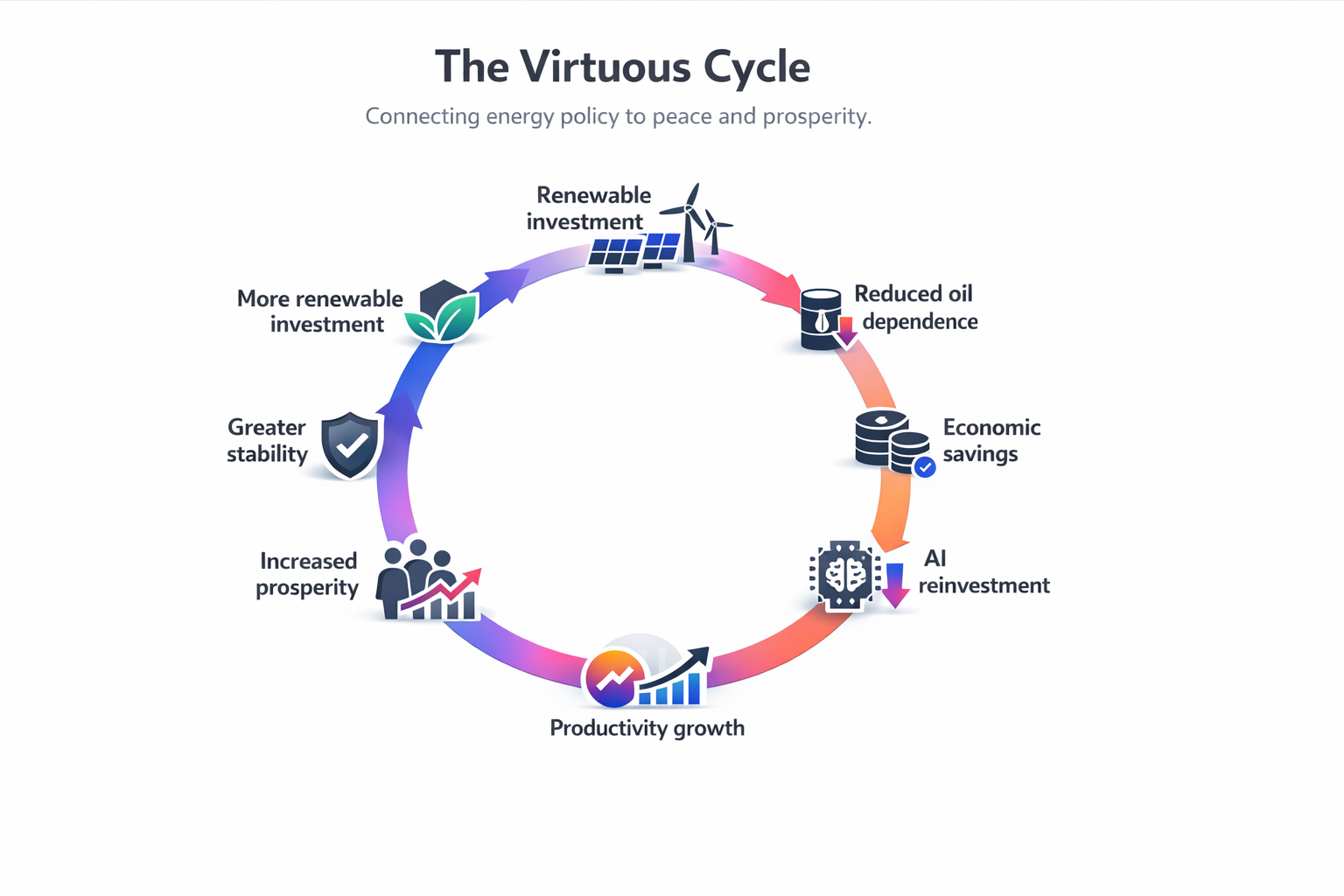
Stage 7 — The Virtuous Cycle
The full Renewable Security Model forms a reinforcing loop:
Renewable investment
Reduced oil dependence
Economic savings
AI reinvestment
Productivity growth
Increased prosperity
Greater stability
More renewable investment
This cycle connects energy policy to peace and prosperity.
Why This Matters Now
Three global trends are converging:
Falling renewable costs
Rapid advances in AI
Increasing geopolitical energy risk
Countries that combine renewables + causal AI decision-making can:
reduce conflict exposure
stabilize their economies
improve public health
increase technological leadership
build long-term prosperity
The Core Idea
Security is no longer defined only by military strength. It is increasingly defined by:
energy independence
economic resilience
technological capability
societal stability
Renewable energy and causal AI together provide a new pathway to peace.
Final Thought
The end of oil wars is not just about replacing fuels. It is about redesigning national strategy.
Renewables reduce vulnerability. AI amplifies productivity. Prosperity strengthens stability. Stability enables peace.
That is the Renewable Security Model.